The security relationship between the United Kingdom and the Islamic Republic of Iran is governed not by visible conflict, but by the absence of verifiable signals in a high-noise environment. When Prime Minister Keir Starmer asserts that there is "no evidence" of Iran currently targeting Britain, he is not describing a state of peace; he is defining the limits of actionable intelligence within a specific kinetic window. Understanding this stance requires deconstructing the Three Pillars of State-Sponsored Subversion: physical proximity, digital penetration, and the utilization of proxy networks.
The current geopolitical friction is a product of the "Threshold Dilemma." In intelligence theory, a threat only becomes a "fact" for public consumption once it crosses the threshold from speculative intent to observable preparation. By stating that no evidence exists, the UK government is signaling that while Iranian intent may remain hostile, the operational capacity to execute an attack on British soil has either been successfully disrupted or has not yet reached a measurable level of maturity. If you found value in this article, you might want to look at: this related article.
The Mechanics of the Intelligence Threshold
Intelligence is a function of probability, not certainty. The UK’s assessment relies on the "Signal-to-Noise Ratio" in counter-terrorism. For a threat to be categorized as "evidence," it must satisfy three criteria:
- Attribution Certainty: The ability to link a specific plot directly to the Islamic Revolutionary Guard Corps (IRGC) or its subsidiaries without ambiguity.
- Resource Allocation: The identification of physical assets, such as funds, weaponry, or personnel, moving toward a specific UK-based target.
- Timeline Maturity: Evidence that a plan has moved from the "conceptualization" phase to the "operational" phase.
When a government claims "no evidence," it often means the activity is currently contained within the conceptualization phase. This is a strategic communication tool designed to lower the temperature of diplomatic relations while maintaining a high state of internal readiness. It serves as a "Negative Signal"—a deliberate move to deny the adversary the satisfaction of knowing their psychological operations are causing domestic alarm. For another angle on this story, check out the recent update from Reuters.
The Cost Function of Iranian Proxy Warfare
Iran rarely utilizes its own sovereign assets for overseas operations. Instead, it employs a "Distributed Risk Model." By leveraging non-state actors and criminal syndicates, Tehran reduces the cost of failure. If a plot is foiled, the diplomatic blowback is mitigated by the lack of direct fingerprints.
The British security services, specifically MI5 and GCHQ, monitor these networks through a process of "Network Mapping." This involves tracking the flow of digital and financial capital from known Iranian hubs to "Sleeper Nodes" within Western Europe. The absence of evidence suggests a temporary "De-escalation Equilibrium." In this state, the cost to Iran of a successful attack—likely a massive retaliatory strike or devastating economic sanctions—outweighs the perceived benefit of silencing a dissident or damaging British infrastructure.
This equilibrium is fragile. It is governed by the $D = (B \times P) - C$ formula, where:
- D is the decision to strike.
- B is the perceived benefit of the attack.
- P is the probability of success.
- C is the cost of retaliation.
Currently, the British government is betting that the C (Cost) remains high enough to keep D (Decision) at zero. However, this assumes the Iranian leadership is a rational actor maximizing for state stability, rather than an ideological actor maximizing for regional influence.
Digital Penetration vs. Kinetic Targeting
While physical threats may be at a low ebb, the "Cyber-Kinetic Intersection" remains a high-activity zone. Iranian state-sponsored groups, such as Charming Kitten or Phosphorus, maintain a persistent presence in British digital infrastructure. The distinction Starmer makes between "targeting Britain" and "general espionage" is critical.
Espionage is the baseline. Targeting implies an intent to destroy, kill, or disrupt. The UK’s defensive strategy relies on "Active Cyber Defence" (ACD). This is not a passive wall but a series of automated systems that identify and neutralize intrusions before they can pivot from data theft to infrastructure sabotage.
The risk of "Cascading Failure" in this sector is significant. A cyber-attack on a UK energy grid or financial hub could be interpreted as a kinetic act of war. By publicly stating there is no evidence of Iranian targeting, the UK is drawing a "Red Line" in the sand. It is effectively saying: "We see your espionage, but do not mistake our tolerance for ignorance. If you transition to targeting, the status quo changes."
The Strategic Utility of the "No Evidence" Narrative
Publicly downplaying a threat serves several tactical purposes for the British state:
- Preservation of Sources and Methods: Acknowledging a threat often requires revealing how that threat was detected. By denying evidence, the UK protects its high-level assets within the Iranian hierarchy.
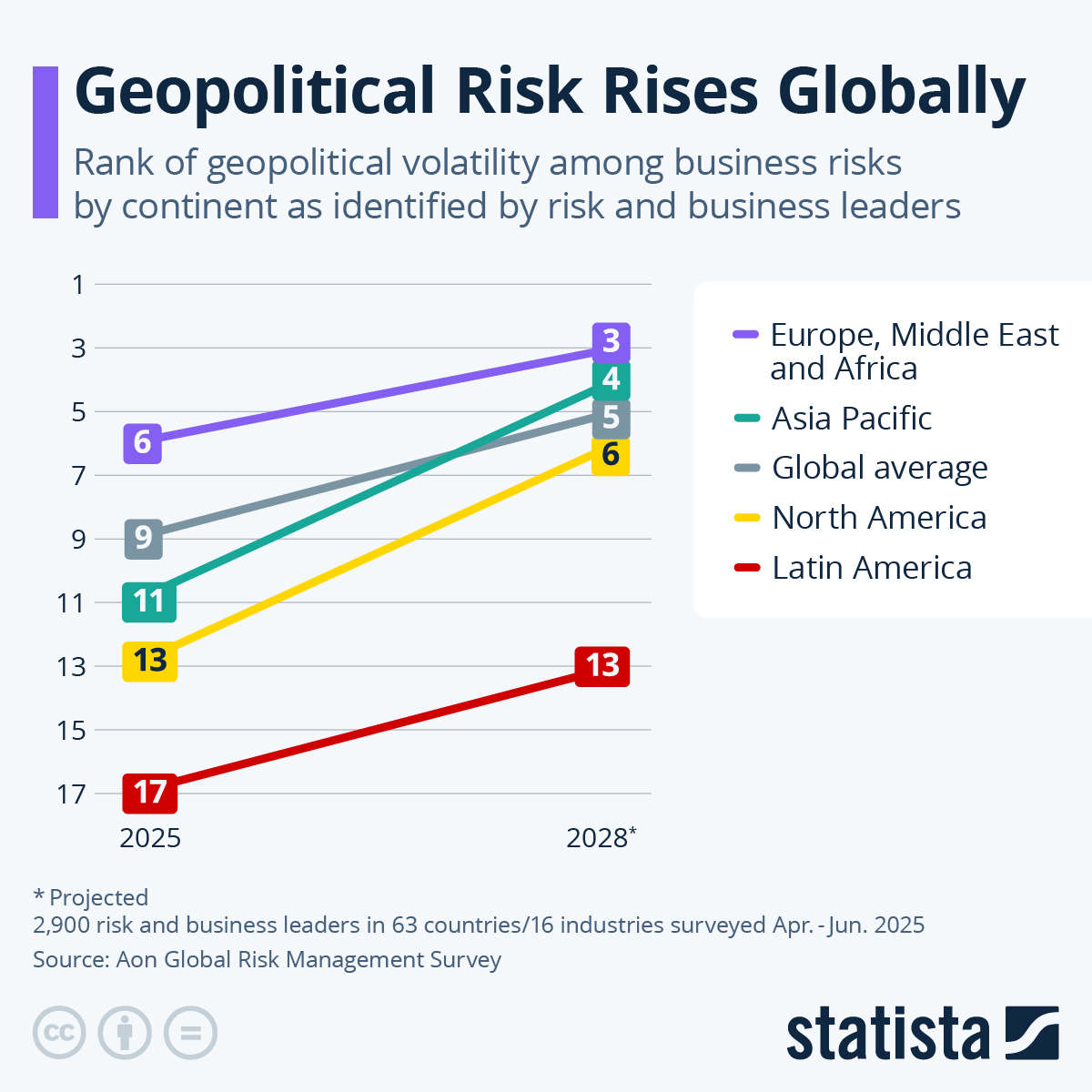
- Economic Stability: Markets react poorly to the prospect of state-sponsored terrorism. Maintaining a narrative of security prevents capital flight and protects the value of the pound against geopolitical volatility.
- Diplomatic Maneuverability: It allows the UK to participate in international negotiations (such as nuclear de-escalation talks) without being forced into a corner by domestic pressure to "do something" about an imminent threat.
The limitation of this strategy is the "Black Swan" event—a threat that exists outside the current monitoring capabilities of the state. If an attack occurs after a "no evidence" declaration, the loss of institutional trust is catastrophic. This creates a "Credibility Debt" that the government must manage with extreme caution.
Structural Vulnerabilities in the UK Defense Posture
Despite the current assessment, two structural bottlenecks remain in the British defense against Iranian influence:
- Transnational Repression Tracking: Iran frequently targets Iranian dissidents living in the UK. Tracking these localized threats requires a level of human intelligence (HUMINT) that is difficult to scale. The "evidence" here is often anecdotal or fragmented, making it hard to meet the Prime Minister's threshold for public acknowledgment.
- Grey Zone Ambiguity: Iran excels in the "Grey Zone"—the space between peace and war. This includes disinformation campaigns and the funding of radicalizing elements within domestic British politics. These activities do not count as "targeting" in a traditional military sense, yet they erode the social cohesion of the state.
The UK's reliance on technical intelligence (SIGINT) means it is excellent at hearing what Iran says, but perhaps less effective at sensing what the "deep state" in Tehran feels. The IRGC operates with a high degree of autonomy, meaning the central government in Tehran may not always be aware of the tactical plans of its sub-units. This creates an "Information Asymmetry" where Starmer may be technically correct that the Iranian state isn't targeting Britain, while elements of the Iranian military are doing exactly that.
Integrated Defense and the Path Forward
To maintain this state of non-evidence, the UK must shift from a "Reactive Detection" model to a "Predictive Analytics" model. This involves using machine learning to parse vast amounts of metadata to identify patterns of "Pre-Operational Surveillance."
The strategic play is not to wait for evidence to appear, but to make the UK such a "Hard Target" that Iranian planners conclude the probability of success (P) is too low to justify the attempt. This requires:
- Hardening of Soft Targets: Increasing the security of dissidents and infrastructure that fall outside of traditional military protection.
- Economic Counter-Messaging: Explicitly linking Iranian financial assets in London to the stability of the current peace.
- Intelligence Reciprocity: Strengthening ties with Five Eyes partners to ensure that a signal missed in London is caught in Washington or Canberra.
The assertion that there is "no evidence" is a snapshot in time, not a permanent condition. It is a declaration of current dominance in the intelligence theater. To ensure this remains true, the British state must treat the absence of evidence not as a sign of safety, but as a mandate for deeper, more invisible vigilance. The goal is to keep the "evidence" in the realm of the theoretical, ensuring that the cost of Iranian aggression remains prohibitively high for the foreseeable future.