The intersection of emerging digital assets and traditional geopolitical lobbying has created a new friction point in international relations. When a 35-year-old cryptocurrency executive facilitates high-level diplomatic access between a nuclear-armed state and a resurgent political administration, it signifies more than a singular networking success. It represents the formalization of "Transactional Access Infrastructure." This model replaces slow-moving institutional statecraft with the high-velocity, high-liquidity mechanisms of the private sector. The efficacy of this approach relies on three specific variables: the erosion of traditional gatekeeping, the alignment of crypto-libertarian ideologies with populist governance, and the exploitation of regulatory grey zones.
The Tri-Node Influence Framework
To understand how a private individual bypasses the State Department, the mechanism must be viewed as a system of three distinct nodes:
- The Liquidity Node: The ability to deploy capital or promise economic revitalization through non-traditional financial sectors (DeFi, Bitcoin mining, digital asset exchanges).
- The Ideological Node: The overlap between the "sovereign individual" ethos of crypto-enthusiasts and the "nationalist-first" stance of specific political factions.
- The Network Node: The utilization of social proof within niche, high-net-worth circles to validate a foreign government's intent.
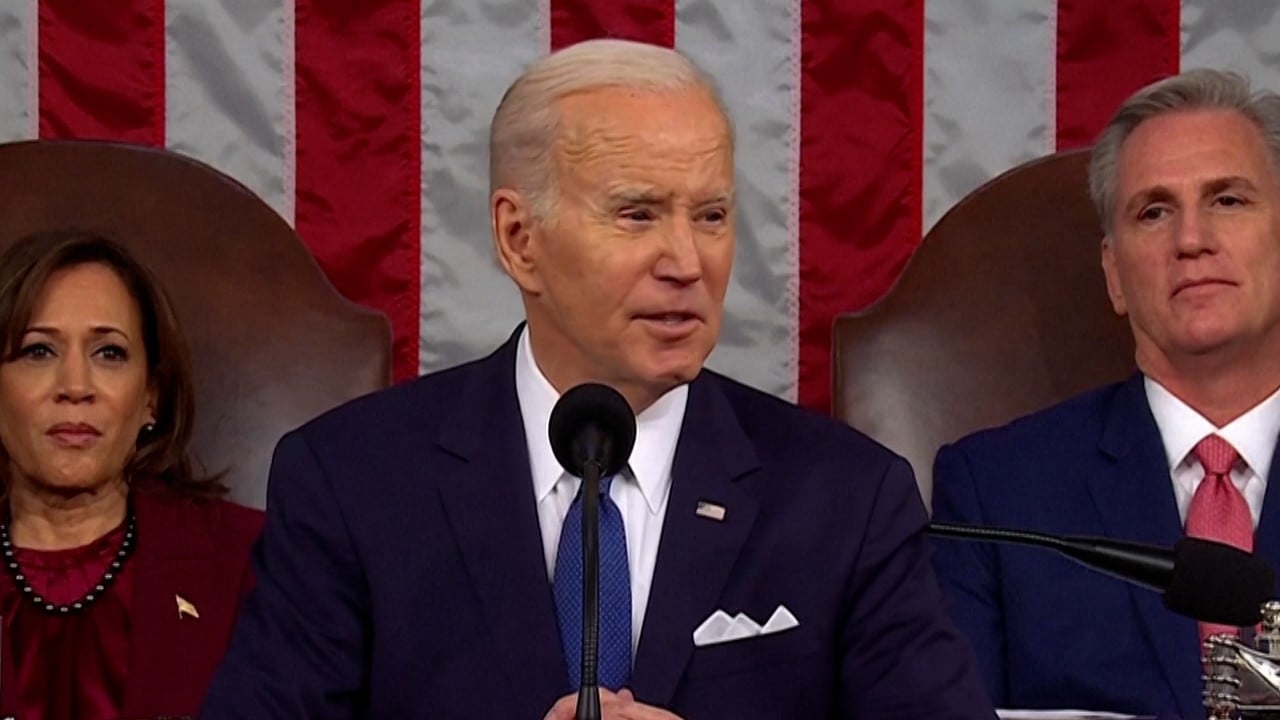
Pakistan’s engagement with the Trump administration through crypto-aligned intermediaries was not a localized event. It was a deployment of the Liquidity-to-Lobbying Pipeline. In this system, the intermediary acts as a risk-mitigator for the political actor, providing a layer of deniability while offering a tangible economic narrative—in this case, the potential for Pakistan to become a hub for digital mining or a partner in circumventing traditional Western financial constraints.
The Cost Function of Modern Statecraft
Traditional diplomacy operates on a high-latency, high-cost model. It requires years of bilateral committee meetings, treaty drafting, and bureaucratic vetting. The "Shadow Diplomacy" model, spearheaded by tech-literate intermediaries, operates on a drastically different cost function.
The efficiency of this model is calculated by the ratio of Access Yield to Bureaucratic Friction. When a private citizen uses a personal relationship with a political figure's inner circle to secure a meeting for a head of state, they are effectively "shorting" the State Department. This creates a market for influence where the currency is not just campaign contributions, but the promise of technological or financial frontier-opening.
The Mechanism of Social Proof Arbitrage
Influence in this context is gained through arbitrage. The intermediary identifies a gap between a country's perceived value and its potential value under a specific regulatory or political shift. By positioning Pakistan as a strategic partner to the "Trump World" ethos—which prioritizes bilateral deals over multilateral institutions—the intermediary rebranded a struggling economy into a "disruption opportunity."
This rebranding relies on Signal Amplification. A crypto executive does not just bring money; they bring a signal of modernity and defiance against the "legacy" financial system. For a political movement that defines itself against the "establishment," this signal is more valuable than a standard diplomatic cable.
Structural Vulnerabilities in Global Gatekeeping
The success of this specific influence operation highlights a systemic decay in the gatekeeping functions of the U.S. executive branch. Historically, the National Security Council (NSC) acted as a filter. However, the rise of "Parallel Channels" has introduced several systemic vulnerabilities:
- Validation Collapse: When informal advisors provide the primary intelligence or networking for a leader, the institutional memory of the civil service is bypassed.
- Information Asymmetry: The intermediary often possesses more specific, real-time data on the digital asset market or the foreign state's internal levers than the official diplomatic corps.
- Alignment Disconnect: The intermediary’s personal profit motive (e.g., securing a crypto license in a developing nation) may diverge from the long-term strategic interests of the home country.
The Pakistani case demonstrates that these vulnerabilities are not bugs but features for those seeking rapid geopolitical repositioning. The intermediary serves as a Transaction Layer, abstracting away the complexities of human rights concerns, nuclear proliferation history, and regional instability in favor of a streamlined "deal-flow" narrative.
The Economics of the Personal Liaison
The financial structure of these arrangements often eludes standard FARA (Foreign Agents Registration Act) filings because the value exchanged is frequently non-monetary or deferred. We define this as The Sweat Equity of Power.
The intermediary invests time and social capital to build a bridge. The "return on investment" comes later, in the form of regulatory favor, introductions to other sovereign wealth funds, or the ability to shape the digital infrastructure of the client state. This is a form of Geo-Economic Front-running. By being the person who "delivered" the relationship, the intermediary secures a permanent seat at the table where future digital asset policy—affecting billions in market cap—will be written.
Logistical Pathing: From Mar-a-Lago to Islamabad
The tactical execution followed a non-linear path. Instead of approaching the U.S. Embassy in Islamabad, the effort targeted the social and digital "periphery" of the administration. This involved:
- Platform Saturation: Using social media and crypto-centric news outlets to build a narrative of Pakistan's "untapped potential."
- Event Proximity: Utilizing high-access physical locations where formal vetting is replaced by social familiarity.
- The Hero Narrative: Framing the outreach not as lobbying, but as a "disruptive" intervention to save a failing relationship between two nations.
This pathing succeeds because it mirrors the decentralized nature of the internet itself. It is a Peer-to-Peer (P2P) Diplomatic Protocol.
Risk Assessment of the Shadow Model
While high-yield in the short term, the shadow diplomacy model carries significant structural risks. The primary failure point is Dependency on Individual Longevity. Unlike institutional relationships, which survive changes in administration, personal-liaison diplomacy is fragile. If the intermediary loses favor or the political actor leaves office, the entire diplomatic bridge collapses, often leaving the client state in a worse position than before.
Furthermore, there is the risk of Regulatory Backlash. As these informal channels become more visible, legislative bodies are likely to introduce stricter definitions of what constitutes "foreign influence." A crypto executive facilitating a meeting between a President and a Prime Minister may soon find their activities classified under expanded lobbying definitions, bringing the very "legacy" scrutiny they sought to avoid.
The Shift Toward Technocratic Feudalism
We are witnessing a transition from traditional Westphalian sovereignty toward a form of Technocratic Feudalism. In this system, individuals with mastery over specific technological or financial domains hold more leverage than career diplomats. Pakistan’s reliance on a crypto intermediary is a symptom of a broader trend where "The Protocol" or "The Platform" becomes the primary engine of international relevance.
States that cannot innovate through traditional channels will increasingly outsource their foreign policy to these digital nomads. This creates a new class of Geopolitical Fixers who operate outside the bounds of traditional accountability. Their power is derived from their ability to translate between the language of the tech elite and the language of populist power.
Quantifying Influence: The New Metrics
To analyze the effectiveness of these actors, we must move beyond "number of meetings held" and look at Metric of Influence Velocity (MIV).
MIV = (Rate of Policy Adoption / Number of Institutional Hurdles Bypassed) * (Market Sentiment Shift)
In the Pakistani instance, the MIV was exceptionally high. The speed at which the narrative shifted from "distrusted regional player" to "strategic tech-ally" in certain influential circles was unprecedented, occurring in a fraction of the time a standard "Charm Offensive" would require.
The Strategic Reorientation
Governments and corporations must adapt to the reality that the most significant diplomatic shifts will no longer occur in the UN General Assembly. They will happen in the DMs of encrypted messaging apps and on the sidelines of tech conferences.
The strategic play for a state like Pakistan—or any emerging economy—is to build a Portfolio of Intermediaries. Relying on a single "Crypto Bro" creates a single point of failure. A diversified approach would involve:
- Establishing formal "Innovation Attachés" who have the cultural competency of the private sector but the accountability of the state.
- Integrating digital asset policy directly into the national security framework to avoid being seen as a "rogue" actor.
- Leveraging the blockchain not just as a financial tool, but as a transparency layer to rebuild institutional trust with traditional allies.
The era of the career diplomat is not over, but it is being aggressively augmented by the era of the high-net-worth facilitator. Those who fail to map these new networks of influence will find themselves locked out of the next generation of global power structures. The move is not to ignore these shadow channels, but to professionalize them before they become the only way to communicate.
Establish a "Geopolitical Risk and Technology" desk that monitors the social-capital movements of key tech executives. Treat their travel and networking patterns as leading indicators of shifting state alliances. The next major trade deal or security pact will likely be signaled by a series of private dinners and social media interactions months before a formal announcement is ever drafted.